This is an update to GitHub Actions Runner on your Kubernetes cluster
Recently, I have been trying to migrate every component in my home lab to be managed by ArgoCD, and GitHub Actions Runner was one of them. While migrating, I found the process to deploy it has changed since last time, and I wouldn’t call it straightforward. So here is an updated note.
Prerequisites
- Kubernetes cluster + ArgoCD
- GitHub organization
- A GitHub repo in the organization to test the runner
Create a GitHub App
There are multiple ways to authenticate the runner with GitHub, but the recommended way is to use a GitHub App. Follow this guide to create one: Authenticating to the GitHub API
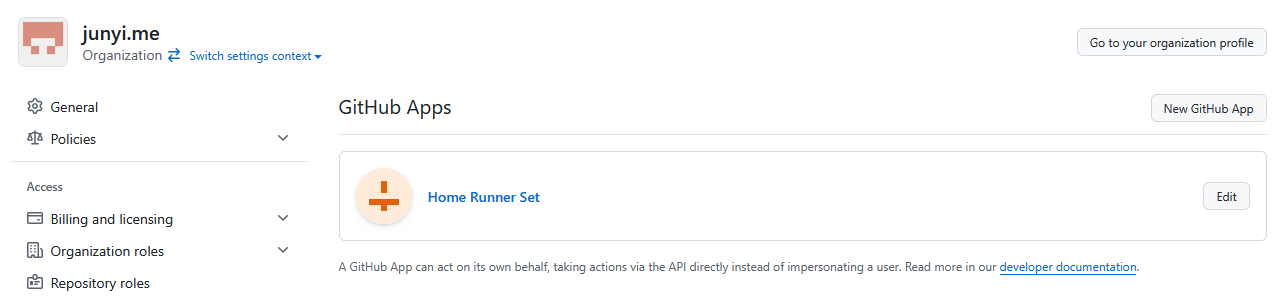
The application will show up like this in your organization:
Keep the following for later steps:
- App ID
- Private key (downloaded as a
.pemfile)
Deploy Actions Runner Controller
We can follow the official guide Quickstart for Actions Runner Controller to set up the ARC, but since I wanted to manage everything declaratively, I created the following ArgoCD application:
|
|
This will deploy the ARC in the gh-arc namespace. You can change the namespace to whatever you prefer.
The chart contains some huge CRD definitions, so the ServerSideApply=true option is required. (See Server Side Apply Option with ArgoCD)
Create a Runner Set
Before deploying the runner set, we need to create a secret with the GitHub App credentials.
|
|
I also created an ArgoCD application for the secret, which just refers to the above yml file in a git repo.
Now we can create the runner set.
|
|
Make sure this is deployed in the same namespace as the secret we created earlier.
Values:
githubConfigUrl: The URL of your GitHub organization or user account.containerMode.type: Set todindif you want to run containerized workloads in the runner. Otherwise leave it out.githubConfigSecret: The name of the secret we created earlier.controllerServiceAccount: the namespace and name of the service account created by ARC.
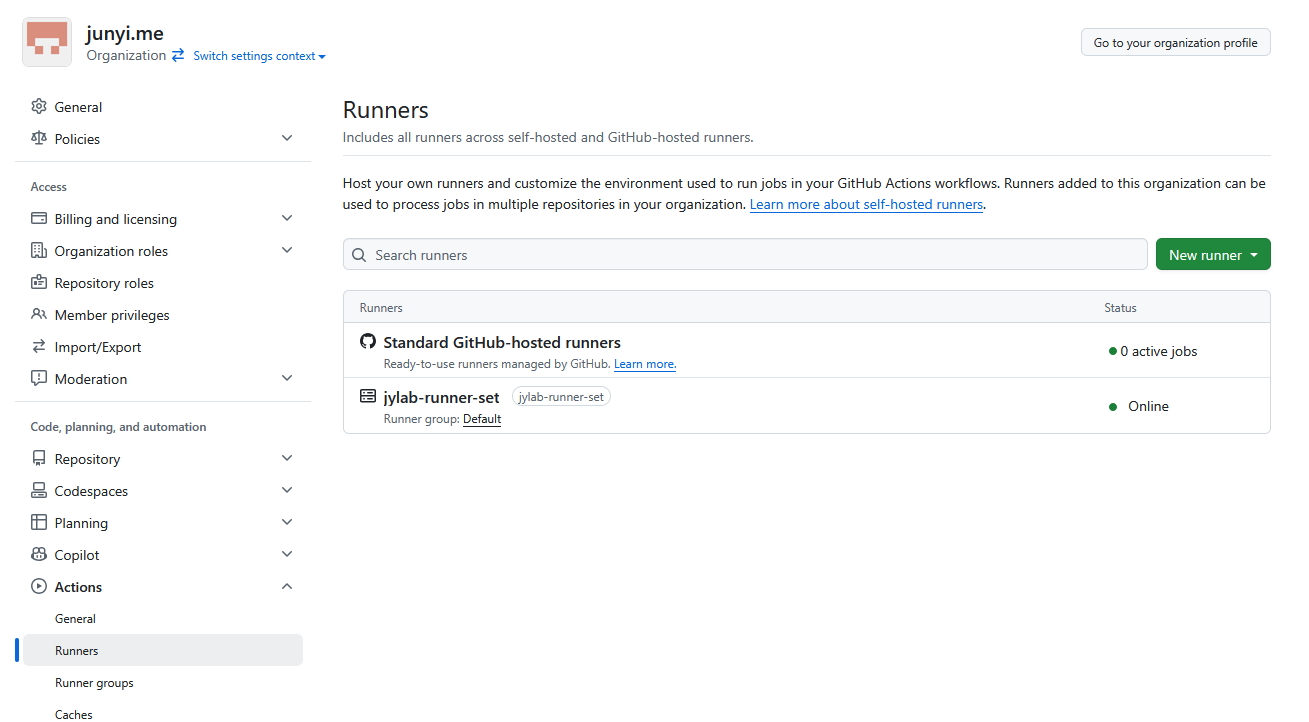
If everything is set up correctly, the runner should be visible in the GitHub organization.
Use ARC from a repository
You can use the runner in any repo in the organization by adding the following to your workflow file:
|
|
Example: docker-build.yml
Conclusion
For some reason, when I tried the previous method of using ARC with personal access token, it didn’t work. So that’s the reason I switched to using a GitHub App. It’s a bit more complex, but it was a good opportunity to switch to a recommended approach.
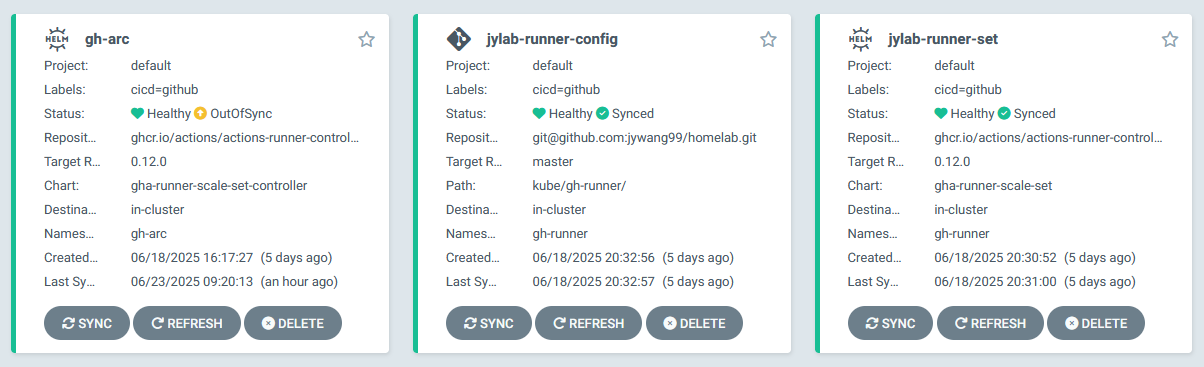
(There are some sync issue with the CRDs defined in gh-arc application that keeps recurring even with auto-sync turned on, but it doesn’t affect the functionality.)
